If your company is comparing IT partners, choosing the right MSP provider is one of the most important decisions you can make. The right fit can help improve security, reduce downtime, support your team, and make everyday technology easier to manage. The wrong fit can leave you with slow response times, unclear responsibilities, and gaps that create risk.
In our most recent episode of Tech Talk, we discussed the kinds of questions and screening items your team should consider when shopping for a Managed Service Provider. That conversation is especially relevant for businesses in the Denver-Arvada area, where organizations need reliable local support but also want a technology partner that can scale with them.
For many Colorado businesses, the search starts with a simple question: What should you actually look for in an MSP provider?
What Is an MSP Provider?
An Managed Service Provider (MSP) is a company that manages and supports part or all of your IT environment. That can include network administration, cybersecurity support, help desk services, software updates, cloud solutions, data backup, and ongoing monitoring.
CBS of Colorado’s managed network services include support such as network hardware and software management, network administration and security, updates, 24/7 help desk access, and transparency around service and accountability. CBS is also a locally owned company based in Arvada and has served Colorado businesses for more than three decades.
That matters because when you choose an MSP provider, you are not just buying a service package. You are choosing a long-term partner that will influence how secure, productive, and resilient your business is.

What Should You Look for in an MSP Provider?
A strong MSP provider should do more than promise support. They should be able to clearly explain how they help your business operate better day to day. Here are some of the most important things to evaluate.
1. Clear Service Scope
Before signing anything, ask exactly what is included. Some companies say they are an MSP provider, but their support is limited. Others offer a broader, more proactive approach.
Your team should understand:
- What is monitored
- What is maintained
- What happens after hours
- Whether cybersecurity is included
- How backups, recovery, and escalation are handled
A good MSP provider should make these answers easy to understand. If the scope feels vague during the sales process, it may feel even vaguer once service begins.
2. Fast, Reliable Support
Response time matters. If your staff cannot log in, access files, print, or communicate with customers, even a short delay can affect revenue and productivity.
CBS of Colorado emphasizes responsive local service and offers 24/7 help desk support as part of its IT services.
For businesses in Denver-metro area, local presence can also be valuable. Remote support is important, but it helps to know your MSP provider understands your market and can be available when hands-on help is needed.
3. A Security-First Mindset
Today, choosing an MSP provider also means evaluating how seriously they take cybersecurity. Federal guidance for businesses stresses the importance of vendor security, access controls, multi-factor authentication, and due diligence when working with third-party technology providers. CISA also notes that using MSPs can expand an organization’s attack surface if risk is not properly managed.
That means your team should ask:
- How do you protect client environments?
- Do you support MFA and access controls?
- How do you handle patching and updates?
- What is your incident response process?
- How do you support backup and disaster recovery?
A dependable MSP provider should welcome those questions.
4. Transparency and Communication
A quality MSP provider should be able to explain recommendations in plain language. You should know what they are doing, why they are doing it, and what your options are.
This is especially important for small and mid-sized businesses that do not have a full internal IT department. You do not want to feel like technology decisions are happening around you without context. You want a partner that helps you make informed decisions.
5. Scalability for Your Business
Your business may look different in one year than it does today. Maybe you will add staff, expand locations, move more systems to the cloud, or strengthen compliance requirements.
The right MSP provider should be able to grow with you. That means their services should support both your current needs and your next phase of growth, without forcing a complete reset later.
Questions to Ask Before You Choose
If your team is actively comparing providers, start with these questions:
- What services are included every month?
- What does your response process look like?
- How do you approach cybersecurity and user training?
- What backup and disaster recovery support do you provide?
- How do you communicate recommendations and issues?
- Can your support scale with our business?
These questions align closely with the screening approach we discussed on Tech Talk because the goal is not just to find an MSP provider. The goal is to find one that fits your business, your risk level, and your expectations.
Why Businesses in the Denver-Metro Should Be Selective
Businesses in the Denver-Metro and the surrounding Colorado market need technology support that is both strategic and practical. A local MSP provider should understand the pace of growing businesses, the importance of quick response, and the value of having a trusted resource nearby.
CBS of Colorado is proud to be a single source for office technology, managed network services, IT support, and related business systems, with its headquarters in Arvada.
That local connection can make a difference when your company wants responsive support and a provider that understands the needs of businesses across the Denver-Metro area with a human-first approach.
Choosing with More Confidence
Choosing an MSP provider shouldn’t come down to price alone. It should factor in clarity, security, responsiveness, and fit. When you ask the right questions early, you put your business in a better position to avoid surprises later.
If your team is evaluating options, start by identifying what support you need most today, where your risks are, and how much guidance you want from a long-term IT partner. That gives you a better framework for comparing any MSP provider and making a smarter decision for the future.
If you are looking for a local partner in the Denver-Arvada area, CBS of Colorado provides managed IT services designed to help businesses improve security, reduce downtime, and get dependable day-to-day support. Contact our team to learn how our managed network services can support your business goals.


 wealth of experience ensures that your business’s IT needs are met efficiently, effectively, and promptly.
wealth of experience ensures that your business’s IT needs are met efficiently, effectively, and promptly.












 High-Speed Output: Kip printers deliver fast, high-quality prints perfect for time-sensitive projects requiring large format output.
High-Speed Output: Kip printers deliver fast, high-quality prints perfect for time-sensitive projects requiring large format output.




 guaranteeing that all businesses can find an office solution that meets and surpasses their needs. This strategic partnership accentuates our dedication to diversifying our offerings and underscores our pledge to equip businesses with top-tier tools essential for their growth and operational excellence.
guaranteeing that all businesses can find an office solution that meets and surpasses their needs. This strategic partnership accentuates our dedication to diversifying our offerings and underscores our pledge to equip businesses with top-tier tools essential for their growth and operational excellence. IT service providers to fortify defenses with state-of-the-art security measures, continuous monitoring, and compliance management, significantly mitigating the risk of data breaches and cyber-attacks.
IT service providers to fortify defenses with state-of-the-art security measures, continuous monitoring, and compliance management, significantly mitigating the risk of data breaches and cyber-attacks.




 management systems can automate repetitive tasks, such as approvals or data entry, accelerating processes and minimizing human error.
management systems can automate repetitive tasks, such as approvals or data entry, accelerating processes and minimizing human error.



 Here’s how MSPs can play a pivotal role in enhancing your business’s cybersecurity in 2023:
Here’s how MSPs can play a pivotal role in enhancing your business’s cybersecurity in 2023:
 Two giants in the field of business printers and copiers, Ricoh and Savin, are now operated exclusively under the name Ricoh. While this may seem like a wrench thrown into your workflow at first glance, the fortunate reality is that not much will change in the way you operate your business’s workflow or service your printers, copiers, and other office hardware. We’ll walk you through what exactly has changed between the Ricoh and Savin brands, and how you’ll approach using and servicing your devices in the future.
Two giants in the field of business printers and copiers, Ricoh and Savin, are now operated exclusively under the name Ricoh. While this may seem like a wrench thrown into your workflow at first glance, the fortunate reality is that not much will change in the way you operate your business’s workflow or service your printers, copiers, and other office hardware. We’ll walk you through what exactly has changed between the Ricoh and Savin brands, and how you’ll approach using and servicing your devices in the future.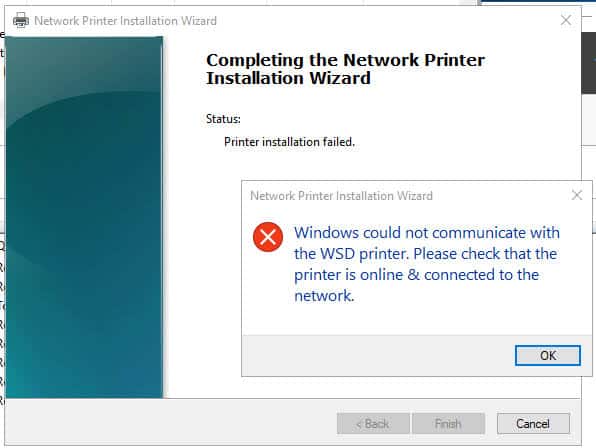 So, What Do All These Have In Common?
So, What Do All These Have In Common?
 When purchasing an office printer or copier, it’s crucial to consider both the upfront and long-term costs associated with the device. Keep in mind the following cost factors:
When purchasing an office printer or copier, it’s crucial to consider both the upfront and long-term costs associated with the device. Keep in mind the following cost factors: Smart Integration from Ricoh, also known as
Smart Integration from Ricoh, also known as 
 In the world of business technology, a Managed Service Provider, or MSP, is a provider of IT and Cloud-based services to businesses and organizations. The advantages of using an MSP lie within two key factors: flexibility, and scalability. An MSP is flexible in that the services they offer may vary in size and scope, depending on your exact needs, and they are scalable by virtue of being able to grow and shrink in size depending on the circumstances at your company at any given time.
In the world of business technology, a Managed Service Provider, or MSP, is a provider of IT and Cloud-based services to businesses and organizations. The advantages of using an MSP lie within two key factors: flexibility, and scalability. An MSP is flexible in that the services they offer may vary in size and scope, depending on your exact needs, and they are scalable by virtue of being able to grow and shrink in size depending on the circumstances at your company at any given time. Complete Business Systems is a proud partner with
Complete Business Systems is a proud partner with  Crexendo VIP Cloud allows you to securely access your phone system from any device, anywhere. This means you can take your business calls on your smartphone, laptop, or desktop computer, making it easy to stay connected and secure no matter where you are. With a traditional PBX, you’re often tied to a specific location or desk phone.
Crexendo VIP Cloud allows you to securely access your phone system from any device, anywhere. This means you can take your business calls on your smartphone, laptop, or desktop computer, making it easy to stay connected and secure no matter where you are. With a traditional PBX, you’re often tied to a specific location or desk phone.
 If you found yourself answering “yes” to the majority, or perhaps even a couple, of these IT security training or IT security technology questions, it may be time to start looking for one or both of them for your business. Look no further than the experts at CBS if your Colorado business needs any sort of IT training or technology — we’ve been in this business for over 25 years, and we’re certified experts at providing IT security support.
If you found yourself answering “yes” to the majority, or perhaps even a couple, of these IT security training or IT security technology questions, it may be time to start looking for one or both of them for your business. Look no further than the experts at CBS if your Colorado business needs any sort of IT training or technology — we’ve been in this business for over 25 years, and we’re certified experts at providing IT security support. If you’re a business owner, you’re no doubt familiar with all the ins and outs of the taxes involved with your business’s operation. Between finding the right equipment, the logistics of purchasing it, and doing all the necessary bookkeeping, it can be a real hassle – but if you know your stuff, you may find your business qualifies for some nice benefits, hidden deep in US tax code.
If you’re a business owner, you’re no doubt familiar with all the ins and outs of the taxes involved with your business’s operation. Between finding the right equipment, the logistics of purchasing it, and doing all the necessary bookkeeping, it can be a real hassle – but if you know your stuff, you may find your business qualifies for some nice benefits, hidden deep in US tax code. True to its name,
True to its name, 
 Most carriers no longer need or want to support aging network infrastructure because they have switched to more modern technologies like fiber optics and mobile/cellular.
Most carriers no longer need or want to support aging network infrastructure because they have switched to more modern technologies like fiber optics and mobile/cellular.