Artificial intelligence can be a powerful tool for improving productivity, automating workflows, and helping teams work more efficiently. But before a business starts plugging AI into its daily operations, there is one important step that cannot be skipped: data hygiene.
At CBS of Colorado, we believe AI should be used strategically, securely, and with a clear understanding of how your business data is organized. That was the focus of our recent Tech Talk with Ray podcast episode, “Data Hygiene: Unlock the Door.” The message is simple: before AI can help your business, your data needs to be clean, organized, protected, and ready.
For Denver Metro businesses exploring AI tools like Microsoft Copilot, automation platforms, or AI-powered workflow solutions, data hygiene is the foundation that helps reduce risk and improve results.
What Is Data Hygiene?
Data hygiene refers to the process of reviewing, organizing, cleaning, securing, and managing business data so it is accurate, accessible, and protected. In practical terms, it means asking questions like:
- Where is our data stored?
- Who has access to it?
- What data is important to our business?
- What files are outdated, duplicated, or unnecessary?
- Is sensitive information properly labeled and protected?
These questions matter because many companies have data scattered across workstations, servers, cloud folders, email inboxes, external drives, and sometimes even old USB drives. Over time, files get duplicated, outdated versions remain in circulation, and employees may have access to folders they no longer need.

That is where data hygiene becomes essential. It helps businesses understand what they have before they give AI tools the ability to interact with that information.
Why Data Hygiene Should Come Before AI Integration
AI tools are only as useful as the data they can access. If your company data is disorganized, outdated, mislabeled, or unsecured, AI may produce unreliable results or expose information to the wrong users.
Strong data hygiene helps create boundaries before AI is introduced. This means your business can decide which files AI should access, which documents should remain restricted, and which workflows are ready for automation.
Without a proper data audit, AI may have access to too much information too quickly. For example, if old employee files, financial documents, client contracts, internal notes, or confidential business records are stored in shared folders without proper permissions, AI tools may be able to surface or summarize information that should not be widely available.
Before integrating AI, Denver businesses should focus on:
- Identifying where business data currently lives
- Categorizing files by importance and sensitivity
- Reviewing employee access permissions
- Removing duplicate or outdated files
- Establishing clear guidelines for AI use
This kind of data hygiene helps your organization move into AI with confidence instead of confusion.
Data Audits Help Protect Your Business
A data audit is the first major step in improving data hygiene. During an audit, your business reviews where files are stored, how they are used, who can access them, and whether they are still relevant.
This process can feel time-consuming at first, but it creates long-term value. A clean data environment makes it easier to manage cybersecurity, document access, backup strategies, disaster recovery, compliance needs, and future automation.
For small and mid-sized businesses in the Denver Metro area, this is especially important. Many teams grow quickly, add new platforms, adopt cloud tools, and adjust workflows over time. Without a structured review, data can become messy without anyone realizing it.
A strong data hygiene plan helps answer key questions before they become problems. Is email being used as file storage? Are important documents backed up? Are there multiple versions of the same file? Are former employees still connected to shared folders? Are sensitive files labeled correctly?
These details matter before AI becomes part of your workflow.
The Role of Access, Labels, and Security
One of the most important parts of data hygiene is access control. Not every employee needs access to every file. A sales team, accounting team, leadership team, and service team may all use different types of data, and each group should only access what is necessary for their role.
Sensitivity labeling can also help businesses classify documents based on importance, confidentiality, and risk. For example, a public marketing document should not be treated the same way as a payroll file, client contract, or internal financial report.
Once files are organized and properly labeled, tools like Microsoft Purview can support sensitivity labeling, auditing, and access management. This can help businesses understand who has accessed a file, who changed it, and whether certain documents should be downloadable or restricted.
This level of data hygiene gives AI tools a safer and more structured environment to work within.
Data Hygiene Also Supports Disaster Recovery
Clean data is not only important for AI. It also makes disaster recovery easier and more effective.
When a company has years of outdated, duplicated, or unnecessary files, backups become more complicated. Businesses may end up storing and protecting data they no longer need while missing the files that are truly critical to operations.
Better data hygiene helps your business identify what needs to be backed up, how often it should be protected, and which systems are most important to restore after an outage, cyber incident, or technical failure.
CBS of Colorado provides IT disaster recovery support, managed network services, hosted cloud services, email security, and document management solutions for local businesses. Our goal is to help companies stay secure, productive, and prepared with practical technology support that fits their needs.
Build Your AI Strategy on a Cleaner Foundation
AI is not going away, and businesses that prepare now will be better positioned to use it wisely. But AI success does not start with the tool itself. It starts with data hygiene.
Before your business adopts AI, take the time to audit your files, organize your systems, review access, label sensitive documents, and create clear internal guidelines. A cleaner data environment helps AI work better, keeps your team aligned, and protects your business from unnecessary risk.
At CBS of Colorado, we take a human-first approach to technology. We help businesses throughout the Denver Metro area understand their current systems, prepare for AI readiness, and build smarter workflows with security in mind. As a locally owned Colorado company serving small and mid-sized businesses for over three decades, CBS provides IT support, managed network services, document management, and office technology solutions designed around real business needs.
Ready to clean up your data before bringing AI into your business? Connect with CBS of Colorado today to start the conversation and build your AI strategy on a secure, organized foundation.




 wealth of experience ensures that your business’s IT needs are met efficiently, effectively, and promptly.
wealth of experience ensures that your business’s IT needs are met efficiently, effectively, and promptly.












 High-Speed Output: Kip printers deliver fast, high-quality prints perfect for time-sensitive projects requiring large format output.
High-Speed Output: Kip printers deliver fast, high-quality prints perfect for time-sensitive projects requiring large format output.




 guaranteeing that all businesses can find an office solution that meets and surpasses their needs. This strategic partnership accentuates our dedication to diversifying our offerings and underscores our pledge to equip businesses with top-tier tools essential for their growth and operational excellence.
guaranteeing that all businesses can find an office solution that meets and surpasses their needs. This strategic partnership accentuates our dedication to diversifying our offerings and underscores our pledge to equip businesses with top-tier tools essential for their growth and operational excellence. IT service providers to fortify defenses with state-of-the-art security measures, continuous monitoring, and compliance management, significantly mitigating the risk of data breaches and cyber-attacks.
IT service providers to fortify defenses with state-of-the-art security measures, continuous monitoring, and compliance management, significantly mitigating the risk of data breaches and cyber-attacks.




 management systems can automate repetitive tasks, such as approvals or data entry, accelerating processes and minimizing human error.
management systems can automate repetitive tasks, such as approvals or data entry, accelerating processes and minimizing human error.



 Here’s how MSPs can play a pivotal role in enhancing your business’s cybersecurity in 2023:
Here’s how MSPs can play a pivotal role in enhancing your business’s cybersecurity in 2023:
 Two giants in the field of business printers and copiers, Ricoh and Savin, are now operated exclusively under the name Ricoh. While this may seem like a wrench thrown into your workflow at first glance, the fortunate reality is that not much will change in the way you operate your business’s workflow or service your printers, copiers, and other office hardware. We’ll walk you through what exactly has changed between the Ricoh and Savin brands, and how you’ll approach using and servicing your devices in the future.
Two giants in the field of business printers and copiers, Ricoh and Savin, are now operated exclusively under the name Ricoh. While this may seem like a wrench thrown into your workflow at first glance, the fortunate reality is that not much will change in the way you operate your business’s workflow or service your printers, copiers, and other office hardware. We’ll walk you through what exactly has changed between the Ricoh and Savin brands, and how you’ll approach using and servicing your devices in the future. So, What Do All These Have In Common?
So, What Do All These Have In Common?
 When purchasing an office printer or copier, it’s crucial to consider both the upfront and long-term costs associated with the device. Keep in mind the following cost factors:
When purchasing an office printer or copier, it’s crucial to consider both the upfront and long-term costs associated with the device. Keep in mind the following cost factors: Smart Integration from Ricoh, also known as
Smart Integration from Ricoh, also known as 
 In the world of business technology, a Managed Service Provider, or MSP, is a provider of IT and Cloud-based services to businesses and organizations. The advantages of using an MSP lie within two key factors: flexibility, and scalability. An MSP is flexible in that the services they offer may vary in size and scope, depending on your exact needs, and they are scalable by virtue of being able to grow and shrink in size depending on the circumstances at your company at any given time.
In the world of business technology, a Managed Service Provider, or MSP, is a provider of IT and Cloud-based services to businesses and organizations. The advantages of using an MSP lie within two key factors: flexibility, and scalability. An MSP is flexible in that the services they offer may vary in size and scope, depending on your exact needs, and they are scalable by virtue of being able to grow and shrink in size depending on the circumstances at your company at any given time. Complete Business Systems is a proud partner with
Complete Business Systems is a proud partner with  Crexendo VIP Cloud allows you to securely access your phone system from any device, anywhere. This means you can take your business calls on your smartphone, laptop, or desktop computer, making it easy to stay connected and secure no matter where you are. With a traditional PBX, you’re often tied to a specific location or desk phone.
Crexendo VIP Cloud allows you to securely access your phone system from any device, anywhere. This means you can take your business calls on your smartphone, laptop, or desktop computer, making it easy to stay connected and secure no matter where you are. With a traditional PBX, you’re often tied to a specific location or desk phone.
 If you found yourself answering “yes” to the majority, or perhaps even a couple, of these IT security training or IT security technology questions, it may be time to start looking for one or both of them for your business. Look no further than the experts at CBS if your Colorado business needs any sort of IT training or technology — we’ve been in this business for over 25 years, and we’re certified experts at providing IT security support.
If you found yourself answering “yes” to the majority, or perhaps even a couple, of these IT security training or IT security technology questions, it may be time to start looking for one or both of them for your business. Look no further than the experts at CBS if your Colorado business needs any sort of IT training or technology — we’ve been in this business for over 25 years, and we’re certified experts at providing IT security support. If you’re a business owner, you’re no doubt familiar with all the ins and outs of the taxes involved with your business’s operation. Between finding the right equipment, the logistics of purchasing it, and doing all the necessary bookkeeping, it can be a real hassle – but if you know your stuff, you may find your business qualifies for some nice benefits, hidden deep in US tax code.
If you’re a business owner, you’re no doubt familiar with all the ins and outs of the taxes involved with your business’s operation. Between finding the right equipment, the logistics of purchasing it, and doing all the necessary bookkeeping, it can be a real hassle – but if you know your stuff, you may find your business qualifies for some nice benefits, hidden deep in US tax code. True to its name,
True to its name, 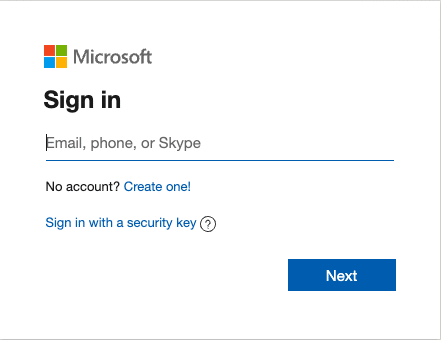
 Most carriers no longer need or want to support aging network infrastructure because they have switched to more modern technologies like fiber optics and mobile/cellular.
Most carriers no longer need or want to support aging network infrastructure because they have switched to more modern technologies like fiber optics and mobile/cellular.